Blockchain Hash Function
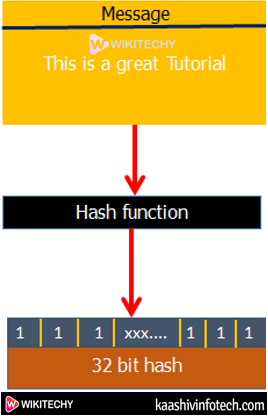
- A hash function takes an input string (numbers, alphabets, media files) of any length and transforms it into a fixed length.
- The fixed bit length can vary (like 32-bit or 64-bit or 128-bit or 256-bit) counting on the hash function which is being used.
- The fixed-length output is named a hash. This hash is additionally the cryptographic byproduct of a hash algorithm.
Blockchain Hash Functions
- The hash algorithm has certain unique properties:
- It produces a singular output (or hash).
- It is a one-way function.
- In the context of cryptocurrencies like Bitcoin, the blockchain uses this cryptographic hash function's properties in its consensus mechanism. A cryptographic hash may be a digest or digital fingerprints of a particular amount of data. In cryptographic hash functions, the transactions are taken as an input and run through a hashing algorithm which provides an output of a fixed size.
Read Also
SHA-256
- A Bitcoin's blockchain uses SHA-256 (Secure Hash Algorithm) hashing algorithm.
- In 2001, SHA-256 Hashing algorithm was developed by the National Security Agency (NSA) within the USA.
How does the hashing process works ?
- This hash function, We are going to use a program developed by Anders Brownworth. This program are often found within the link.
Anders Brownworth Hash Program

SHA256
- If we type any character within the data section, we'll observe its corresponding cryptographic hash within the hash section.
- For example: We've type in data section: This is a great tutorial.
- It will generate the corresponding Hash:
759831720aa978c890b11f62ae49d2417f600f26aaa51b3291a8d21a4216582a

SHA256
- Now if we change the text: "This is a great tutorial." To "this is a great tutorial."
- You will find the corresponding Hash:
4bc35380792eb7884df411ade1fa5fc3e82ab2da76f76dc83e1baecf48d60018 - In the above, you can see that we have changed only the first character case sentence from capital "T" to small "t" and it will change the whole Hash value.
- Since the Hash function may be a one-way function, there's no way to get back entire text from the generated hash. This is often different from traditional cryptographic functions like encryption where you'll encrypt something using the key and by using decryption, you'll decrypt the message to its original form.
Advantages
- Main advantage is synchronization.
- In many situations, hash function turn out to be more efficient than search trees or the other table lookup structure. For this reason, they're widely used in many types of computer softwares, particularly for associative arrays, database indexing, caches and sets .
Disadvantages
- Hash collisions are practically unavoidable. When hashing a random subset of an oversized set of possible keys.
- Hash function become quite inefficient when there are many collisions.
- Hash function doesn't allow null values, like hash map.
