Bitcoin Mitigating Attacks
Bitcoin Mitigating Attacks
- Bitcoin is that the most secure cryptocurrency, which give security at multiple levels of the protocol.
- It also rendering sustained sophisticated attacks.
- We are going to check out various types of probable attacks within the bitcoin system.
The Sybil Attack
- The Sybil attack happens within the peer-to-peer network. A malicious attacker wishes to hold out this attack on the bitcoin network.
- A node within the network operates multiple identities at an equivalent time and undermines the authority in the reputation system.
- Its main aim is to realize the majority of influence within the network to hold out illegal actions within the system.
- The Sybil attack is difficult to detect and prevent, but the following measures are often useful:
- By increasing the price of making a new identity.
- Require validation of identities or trust for joining the network.
- Give different power to different members.
Read Also
Race Attack
- The Race Attack requires the recipients to simply accept unconfirmed transactions as payment. As an attacker, you'll send the same coin to different vendors by using the 2 different machines.
- If the vendors do not wait for the block confirmation delivering the items, they're going to soon realize that the transaction was rejected during the mining process. The answer to the present is that the vendor must wait a minimum of one block confirmation before sending out things.
- This attack is easier to pull off when the attacker features a direct connection to the victim's node. It's recommended to turn off incoming connections to nodes for receiving payments in order that your node will identify their own peers. And it doesn't allow the payer to submit the payment to the payee directly.
Finney Attack
- The Finney attack is named as after Hal Finney. The Finney attack is one among the types of double-spending problem.
- During this attack, the attacker is that the miner who mines blocks normally. Within the block, he includes a transaction which sends a number of his coins back to himself without broadcasting the transaction.
- When he finds a pre-mined block, he sends the same coins in a second transaction. The second transaction would be rejected by other miners, but this will take some time.
- To stop this attack, the seller should await a minimum of six blocks confirmation before releasing the goods.
Vector76 Attack
- The Vector76 attack may be a combination of the Race attack and therefore the Finney attack such a transaction that even has one confirmation can still be reversed.
- A miner creates two nodes, one among which is connected to the exchange node, and therefore the other is connected to well-connected peers within the block chain network.
- The miner creates two transactions, one high value, and one low value. The attacker pre-mines a high-value transaction to an exchange service. When a block is announced, he quickly sends the pre-mined block on to the exchange service.
- When exchange service confirms the high-value transaction, the corrupted attacker sends a low-value transaction to the block chain network that finally rejects the high-value transaction.
- As a result, the corrupted attacker's account is deposited on the quantity of the high-value transaction. This attack are often protected by disabling the incoming connections and only connecting to well-connected nodes.
The 51% Attack
- The 51% attack may be a potential attack on the blockchain network.
- It refers to one miner or group of miners who try to regulate more than 51% of a network's mining power, computing power or hash rate. The attacker can block new transactions from happening or being confirmed.
- They're also ready to reverse the transactions that have already confirmed while they were in control of the network, leading to a double-spending problem.
- When a miner forms a valid block of transactions, the individual will broadcast the block to other miners on the network. It can only be accepted if all transactions during a block are valid according to the exiting record on a blockchain.
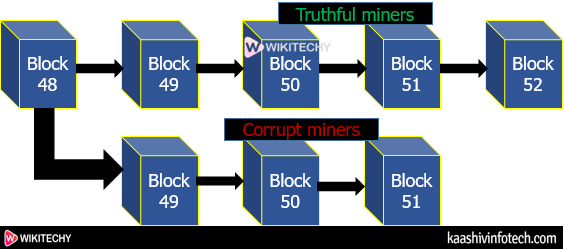
- A corrupt minor with more than 50% of a network's hash rate doesn't broadcast solutions to the rest of the network. It leads to the formation of two versions of the blockchain.
- One is that the public version of the blockchain, which is being followed by legitimate miners.
- Second is used by the corrupt miners who aren't broadcasting it to the rest of the network.
Bitcoin Mitigating Attacks
- This type of attack is fictitious because it is costly to acquire computing power, which has more than 50% of the computing power of the entire network
